Recon is such a critical part of penetration testing and is so important it’s been incorporated into frameworks such as OSSTMM, PTES, NIST SP800-115. But why does it need to be strictly for penetration testing? One of the main reasons I love red team training and CTFs is so I can leverage the knowledge as a defender and this is a perfect example. Blue teams can and should leverage recon techniques for their environment too!
In this post, I’d like to talk about some of the tools I like to use as a security engineer in my day job. For me, the key to defending my environment is gaining visibility and also actively looking for vulnerabilities or gaps the same way an attacker would.
1. Shodan and Censys
Shodan is a an amazing internet scanner which essentially scans everything internet facing. I’d definitely recommend spending some time Shodan surfing and searching for internet facing infrastructure related to your environment. There’s also a ton of search terms similar to google dorking for better searches as well.

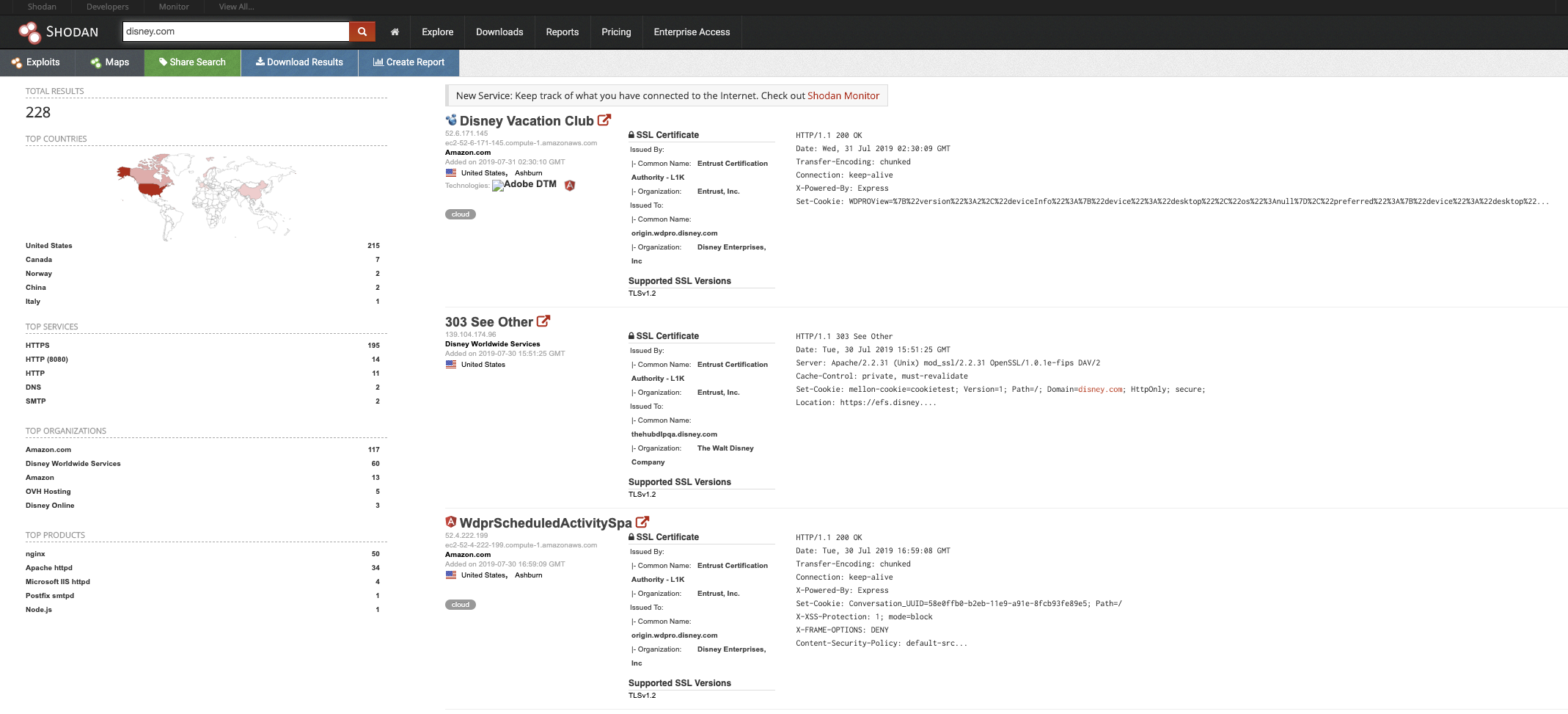
You can also leverage Censys.io as well which is another phenomenal site for this!

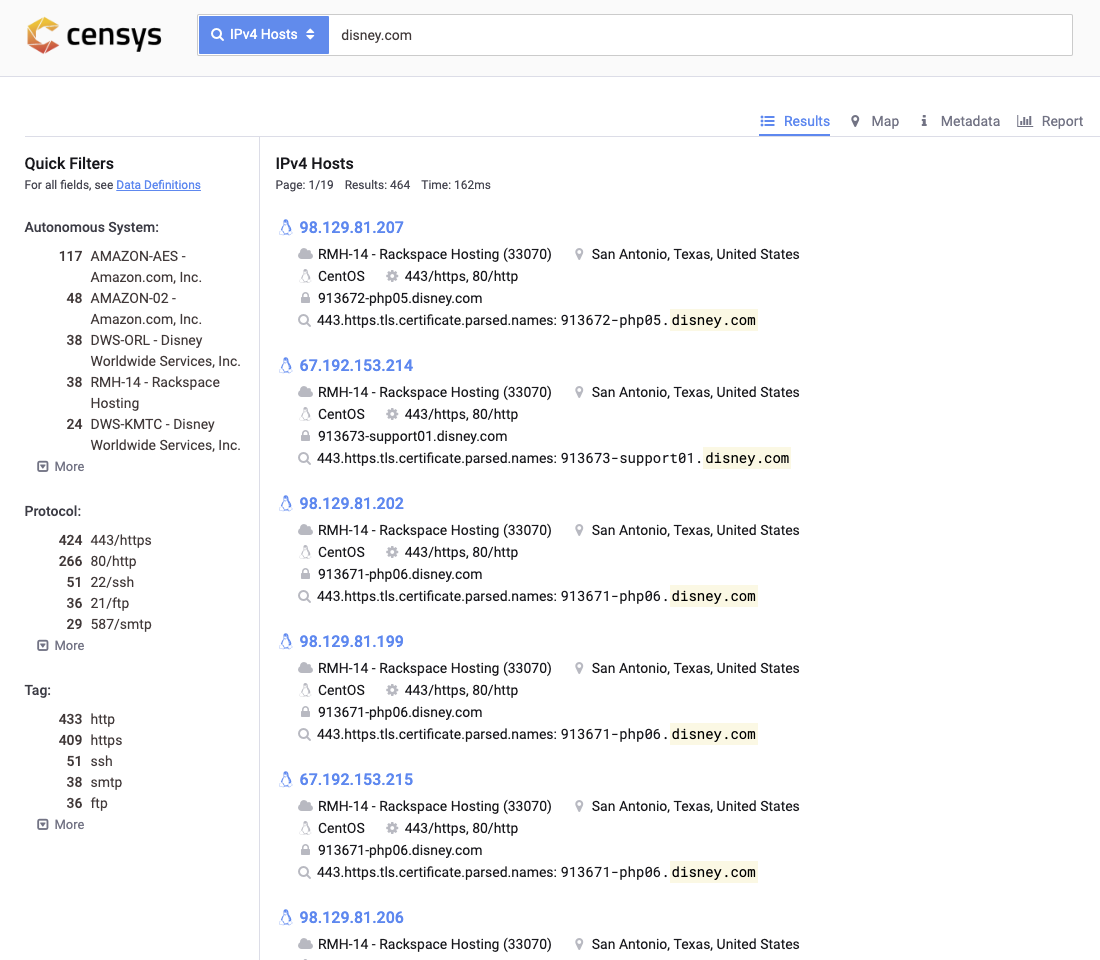
These tools are GREAT and can give you some visibility on your internet facing infrastructure. Definitely check it out and make sure there’s no odd ports enabled or systems that shouldn’t even be internet facing!
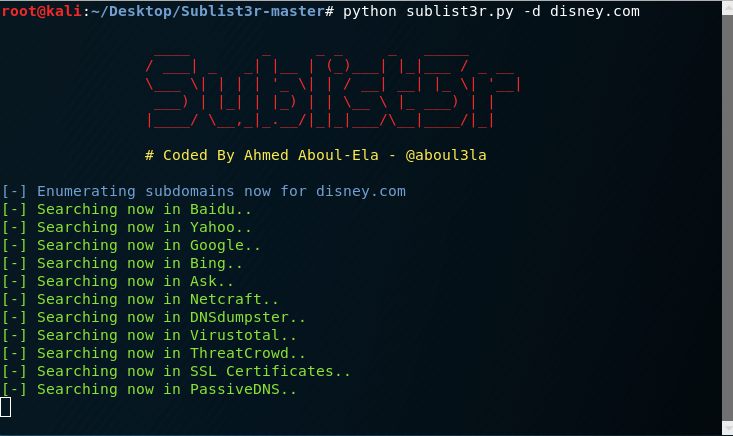
2. Sublist3r
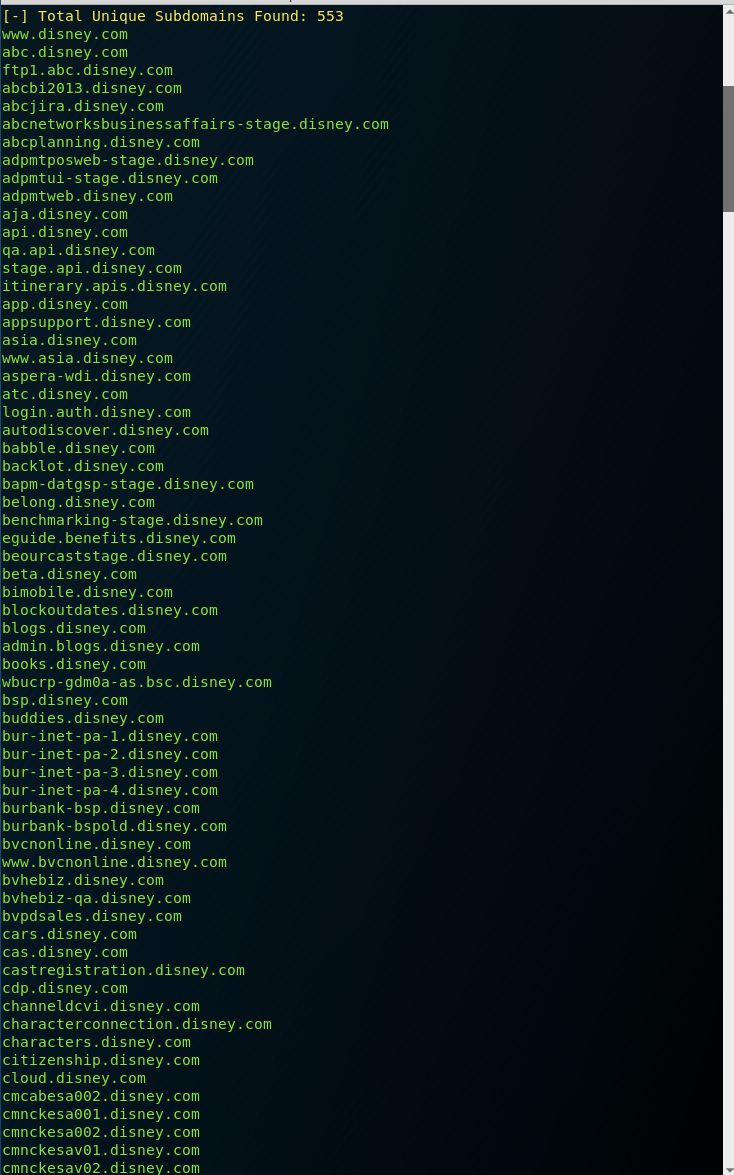
Sublist3r has been my subdomain enumeration tool for the longest time and is definitely my go-to. I definitely recommend leveraging this tool as a defender to get a better view of all the subdomains your organization might own. It’s completely passive so you’re not going to take out production systems either.
Look at all the subdomains below! That’s not even the full list!
Amass is another subdomain enumeration tool that’s caught my attention lately as well. I don’t have a lot of experience with it just yet, but will start incorporating it and may possibly replace Sublist3r. These tools are so fun and it’s definitely like finding buried treasure sometimes!
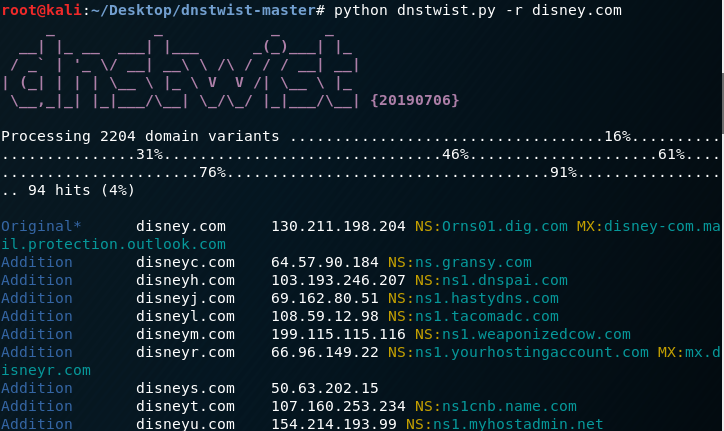
3. DNStwist and UrlCrazy
DNStwist is also another fun tool I use in my day job. This tool allows you to find phishing sites, typosquatting or fraudulent/knockoff sites!
Similarly, Urlcrazy can also detect phishing sites, typosquatting and other interesting things.
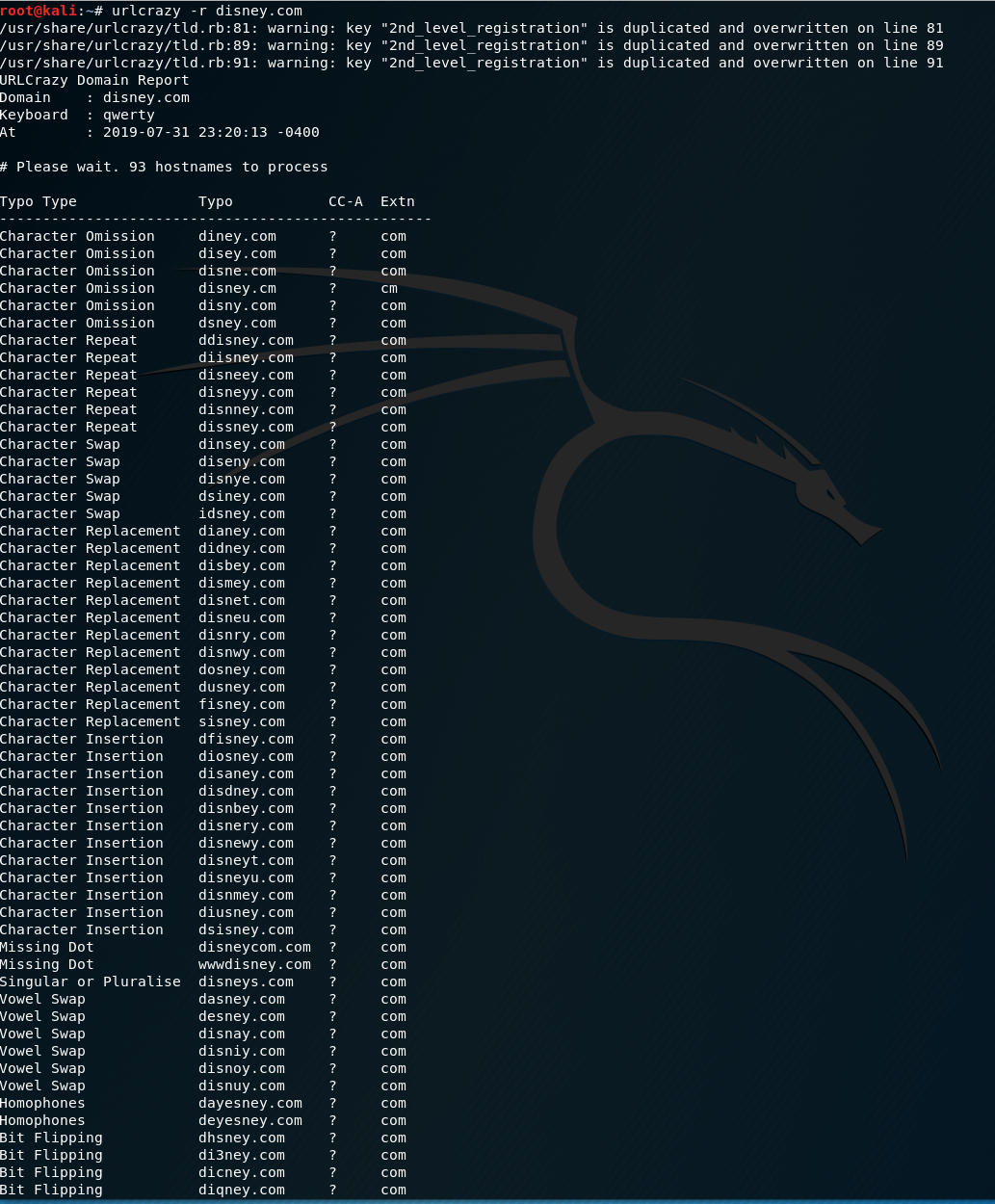
Bonus points for scripting these two tools to run on a weekly basis! This can definitely help supplement services that companies like MarkMonitor offer.
These are just some examples of things I like to do to actively poke at my environment and make sure we have the visibility. I didn’t even touch on enumerating internal environments with tools like nmap and bloodhound but these are things the “bad guys” can use to “case the joint” so to speak. Play with these tools and show the red teamers that blue teams can be cool too!