Some of the best experiences of my life would hands down have to be the SANS NetWars capture the flag (CTF) events! I’ve been very fortunate to be able pay my way through SANS trainings and figured I’d give this a shot as well. Aside from hackthebox.eu, I am fairly green when it comes to CTF events and wanted to just dive in to learn as much as possible.
The NetWars events are usually at larger SANS conferences and are free with a 5-6 day course so they’re definitely a good value.
There’s a few different variations of the NetWars challenges with some being Cyber Defense, Core, DFIR and ICS to name a few. Each has their own set of challenges and are usually themed! The events I’ve done were for the Core variation which is big on the following topics:
- Vulnerability Assessment
- Packet Analysis
- Penetration Testing
- System Hardening
- Malware Analysis
- Digital Forensics and Incident Response
There’s 5 levels of challenges which really makes it a fun competition!

My first NetWars event was at SANS Network Security 2018. I had registered for the Network Penetration Testing and Ethical Hacking course (SEC560 / GPEN) and figured I’d do a CTF as well since it was a free add on. The event was over two nights and was in two 3 hour blocks after class (6:30pm – 9:30pm). You’re able to play solo or in a team! I managed to meet with some friendly security pros and we formed a team of 5.

I didn’t really know what to expect going in, but wow it was an experience! You’re given a USB with a Linux image to play off of. The first two levels are played locally and levels 3-5 require a VPN connection (which you must solve to get!)

To play the game, you have to log in to your account on CounterHackChallenges (https://www.counterhackchallenges.com/) where you’re asked questions related to your event. The questions require you to think on your feet and really challenge your skills in incident response and forensics at first. Level 3 is where you start to get offensive and hack your way into a DMZ and then pivot into an internal network.
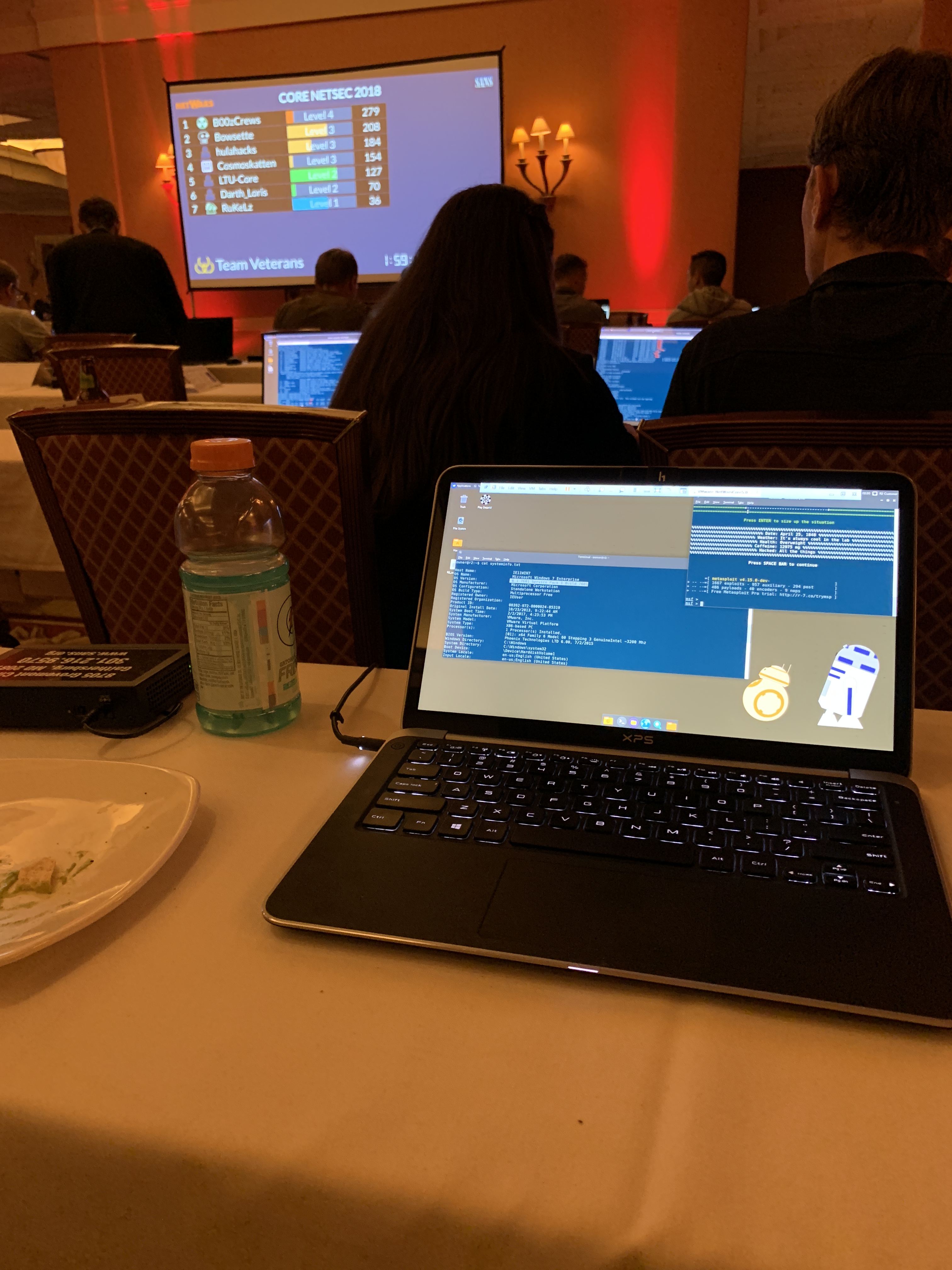
It was such a good feeling every time we answered a question correctly! By the end of the event, we finished in the top 10 on the leaderboard for new teams. We also made it to level 3! It was such an accomplishment for myself! At the end of the event you receive an individual scorecard showing your strengths and weaknesses. I definitely learned a lot in addition to the actual SANS course I was taking!

Last May I was really fortunate enough to get the time off work in order to go to SANS Security West 2019 this year. Since I was doing Web Application Penetration Testing and Ethical Hacking (SEC542 / GWAPT) I knew I had to register for NetWars again! It’s seriously my favorite part of the SANS events and made the pain in my wallet worth it!

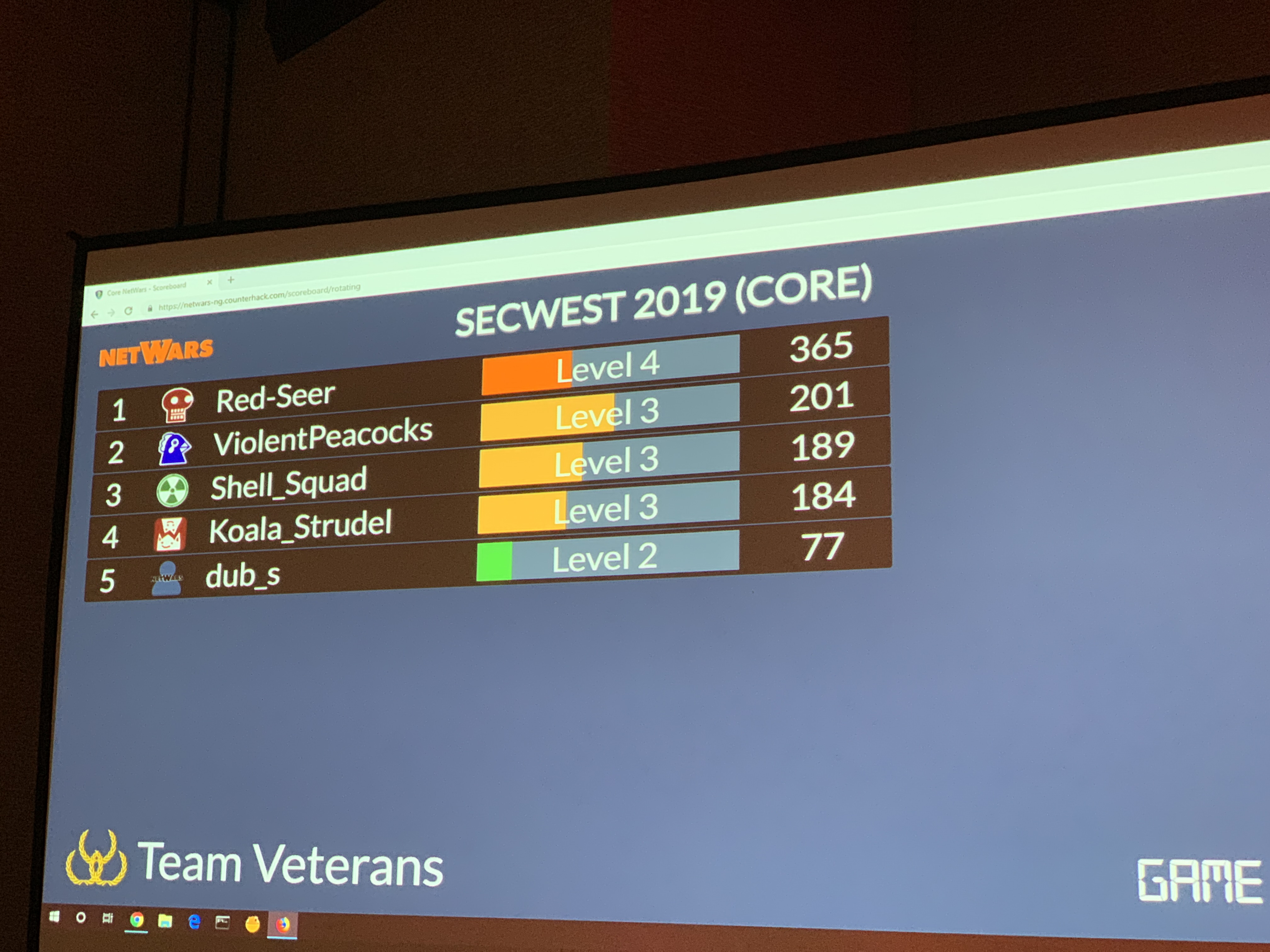
This time though I was able to go to the event with one of my best friends! He was taking the GCFA course and is super strong in forensics and incident response. We both signed up for Core NetWars and decided to try our best to win and just have fun! Without him, I definitely wouldn’t have learned some cool packet analysis and memory analysis techniques and tools!



We ended up powering through many of the questions over the two nights. After all was said and done, we ended up in 2nd place at level 3! Team ViolentPeacocks!

If you’re ever attending a SANS Event – I highly recommend registering for NetWars if available! I learned so much and that was on top of the actual SANS course itself!
You can see more on NetWars from the SANS site here: https://www.sans.org/netwars/
Note: I am not affiliated with SANS but really enjoy their specialized information security training.