I just finished up dealing with some pretty nasty alerts and events today at work and it got me thinking about this topic.
Endpoint detection and response (EDR) tools have been around for awhile now and are really changing the landscape for defenders. They give incident handlers and security analysts so much information and abilities. I will go out and say it: EDR is a necessity.
The main reason I say EDR is a necessary tool nowadays is just for one simple fact – They are a force multiplier for security teams.
Think about it: they give security teams the ability to start an investigation, dump memory remotely, put or get files, kill processes or even isolate the endpoint! Before this, it was a little harder to get all these abilities without having to use multiple tools and involving IT.
I sometimes think back on what life was like before EDR and wonder how I ever survived (kidding). In my day to day, investigating incidents is so much easier and way more fun with EDR. I get to look at all the data with our SIEM and then move into our EDR to dive into endpoint processes, dump memory remotely, or even isolate the endpoint when something looks particularly nasty.

Being able to see the process tree really helps put context and color on what happened when working an investigation.
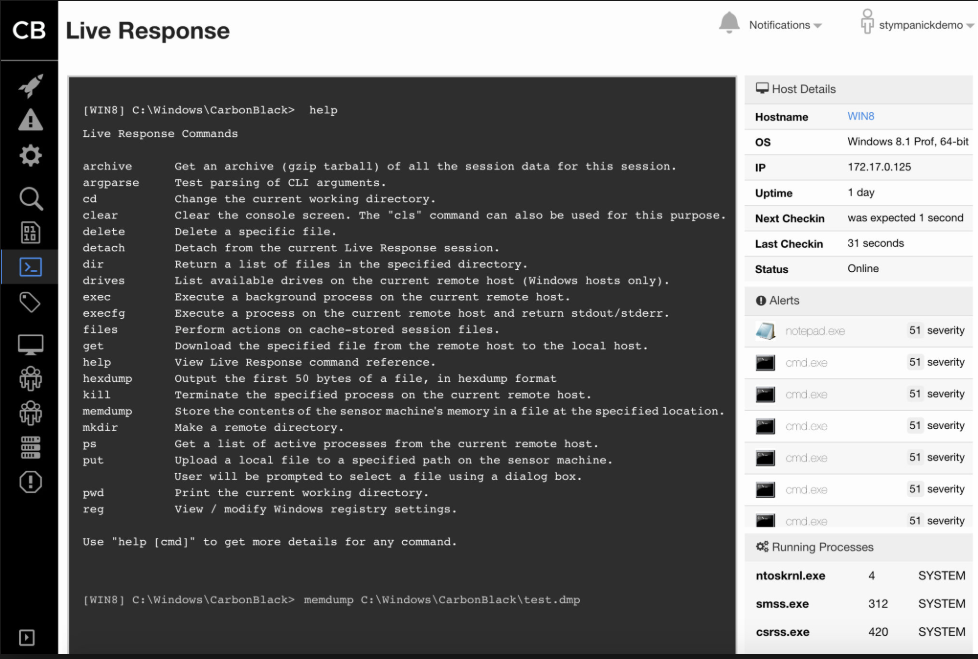
By far, the best thing about EDR is the power it gives you as an incident handler. Look at all the nifty features available in the screenshot above. For this alone, I say it becomes a security team’s strongest weapon.
I’m just speaking from my experience and really think EDR is a necessity nowadays. I’m sure some EDR solutions are better than others but you really should think about leveraging any EDR tool if you’re not already.
Thanks for reading!