I love finding out about tools and messing around with them. Today let’s talk about Sherlock.
Sherlock is a powerful OSINT tool for searching usernames on social media (https://github.com/sherlock-project/sherlock). It’s super quick to install and even easier to use. Let ‘s check it out.
First we start with installing it:
# clone the repo
$ git clone https://github.com/sherlock-project/sherlock.git
# change the working directory to sherlock
$ cd sherlock
# install the requirements
$ python3 -m pip install -r requirements.txtNow that we have the out of the way. We can start hunting for accounts!
Let’s hunt for a popular YouTuber’s accounts:
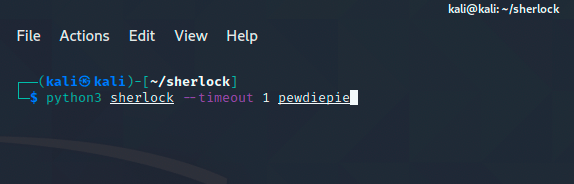
In the above image, we’re running the sherlock command with the timeout flag set at 1 second for a quick scan.
Let’s see what accounts are named PewDiePie.
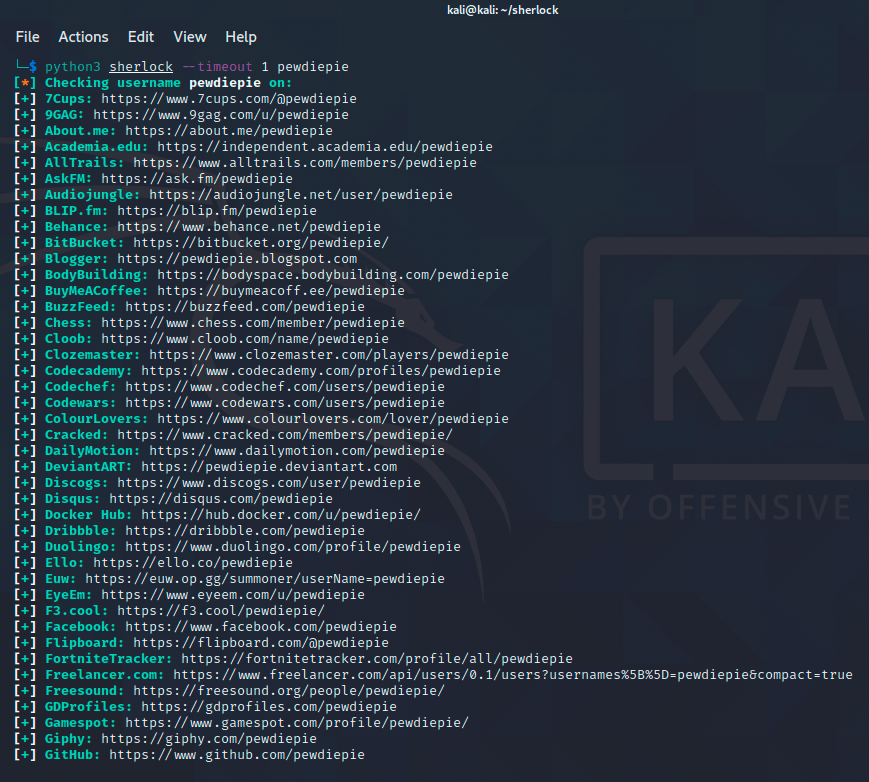
Whoa! There’s quite a few accounts out there! Let’s hunt for another account.
How about checking out an awesome security professional? Let’s see what we can dig up.
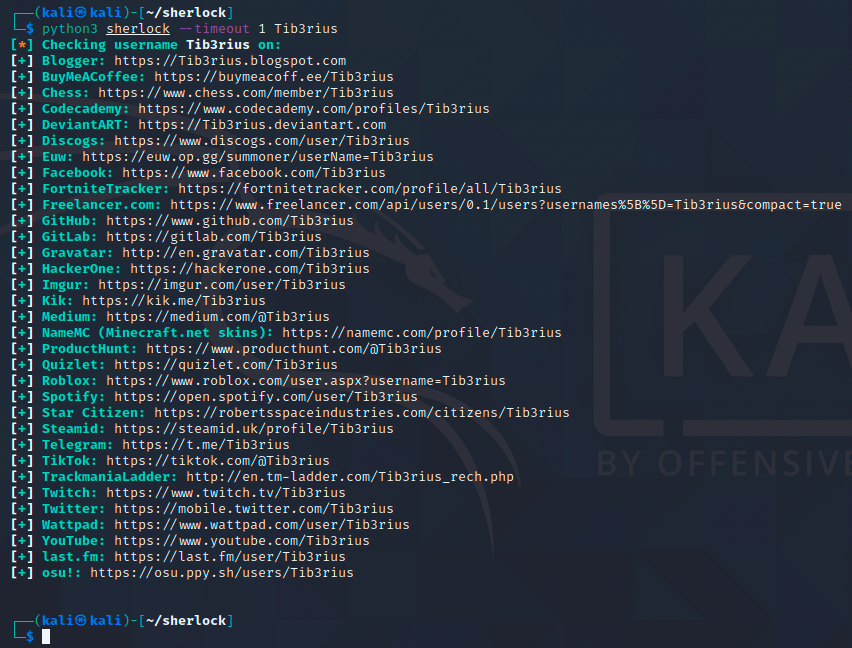
Nice! Here we’ve found several accounts belonging to Tib3rius!
OSINT is always a bit creepy but can also be a powerful defense tool for you or your org. I recommend checking out other OSINT tools like recon-ng, creepy or even something like searchcode (to get a feel of an org’s development footprint). I’ll most likely use this tool on myself to keep my digital footprint in check (as much as possible at least).